Trezor Login: Effortless and Secure Access
Easily and safely log in to your Trezor hardware wallet to manage your cryptocurrency portfolio with confidence using the official Trezor Login.
Introduction to Trezor Login
Trezor Login is the official method to securely access your Trezor hardware wallet. It allows users to manage multiple cryptocurrencies, monitor balances, and perform transactions while keeping private keys offline.
Using the official login ensures protection against phishing attacks, malware, and unauthorized access attempts.
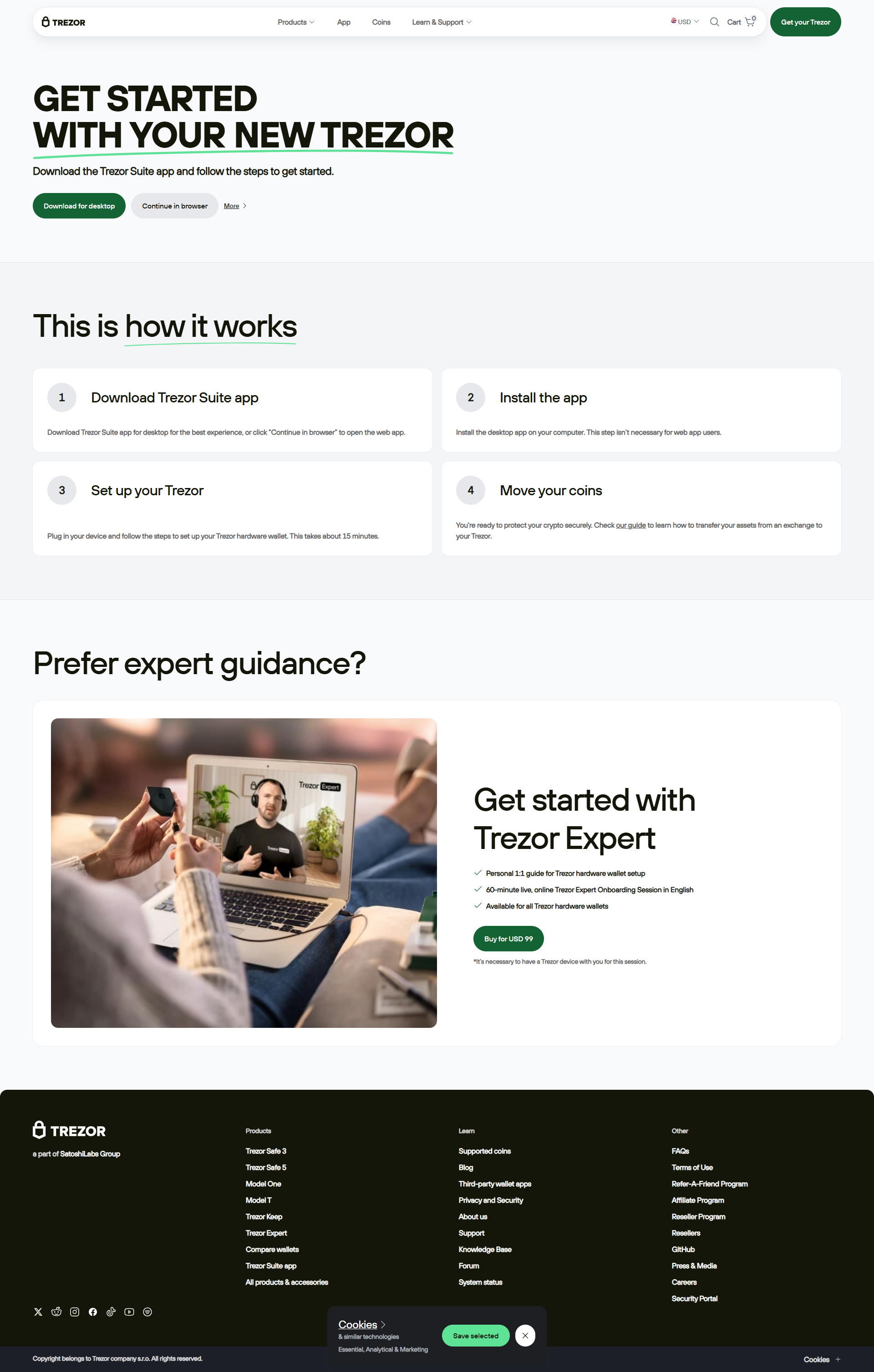
Step-by-Step Login Process
Step 1: Visit Official Trezor Interface
Open your browser and navigate to the official Trezor login page to start a secure session.
Step 2: Connect Your Trezor Device
Plug your Trezor wallet into your desktop or mobile device to establish a secure connection.
Step 3: Enter Your PIN
Enter the PIN you configured during wallet setup to securely unlock your wallet.
Step 4: Access Your Wallet
Once logged in, manage your crypto portfolio, send and receive funds, and review balances safely.
Benefits of Using Official Trezor Login
Logging in through the official Trezor interface ensures your private keys remain offline, protecting your digital assets from phishing attacks and unauthorized access.
Key Features
- Official Access: Only use verified channels for login.
- Hardware Security: Private keys never leave your Trezor device.
- Manage Multiple Assets: Safely monitor and transact with various cryptocurrencies.
- Anti-Phishing Protection: Protect your wallet from malicious websites.
- Cross-Platform Login: Access securely from desktop or mobile devices.
FAQs
Q: Can I log in from different devices?
Yes, official Trezor Login allows secure access from multiple devices while keeping your private keys offline.
Q: What if I forget my PIN?
Reset your device and restore access using your recovery seed.
Q: Is my crypto safe during login?
Yes, private keys remain on the hardware device, ensuring full security throughout the login process.
Trezor Login vs Third-Party Access
Securely Access Your Wallet Today
Using the official Trezor Login ensures safe access to your hardware wallet. Log in confidently, manage your portfolio, and protect your cryptocurrency assets from unauthorized access right from your first login.